
3 AI Security Audit Tools That Will Not Make You Nap
Why Slow Security Scans Are Killing Your DevSecOps Workflow
A blazing fast vuln scanner is the difference between security that actually ships with your code and security that gets skipped because nobody has time to wait.
Here are the top picks covered in this article:
| Tool | Best For | Speed Highlight |
|---|---|---|
| aiscan | AI/LLM codebases | 100k LOC in under 5 seconds |
| xssprober | XSS and web entry points | Scan time independent of parameter count |
| Grype | Containers and supply chain | Results in seconds; SBOM rescans skip image re-analysis |
All three tools are free and open source.
Here’s the uncomfortable truth: most security scans are too slow to fit into a real CI/CD pipeline. Developers skip them, delay them, or run them overnight when nobody’s watching.
The result? Vulnerabilities like XSS, exposed secrets, and CVEs slip into production.
Speed isn’t just a nice-to-have. Without it, security tools don’t get used. Security engineering experts have noted that without speed, developers simply can’t integrate scanners into CI pipelines or iterate on rules efficiently. That’s why the modern generation of scanners is built around one core idea: scan faster, find more, block less of your team’s time.
The tools in this roundup take very different approaches to speed. One uses parallel Rust processing and tree-sitter parsing. Another injects payloads into every parameter in a single HTTP request. A third skips re-analyzing images entirely by scanning SBOMs instead. Each approach solves a real bottleneck.
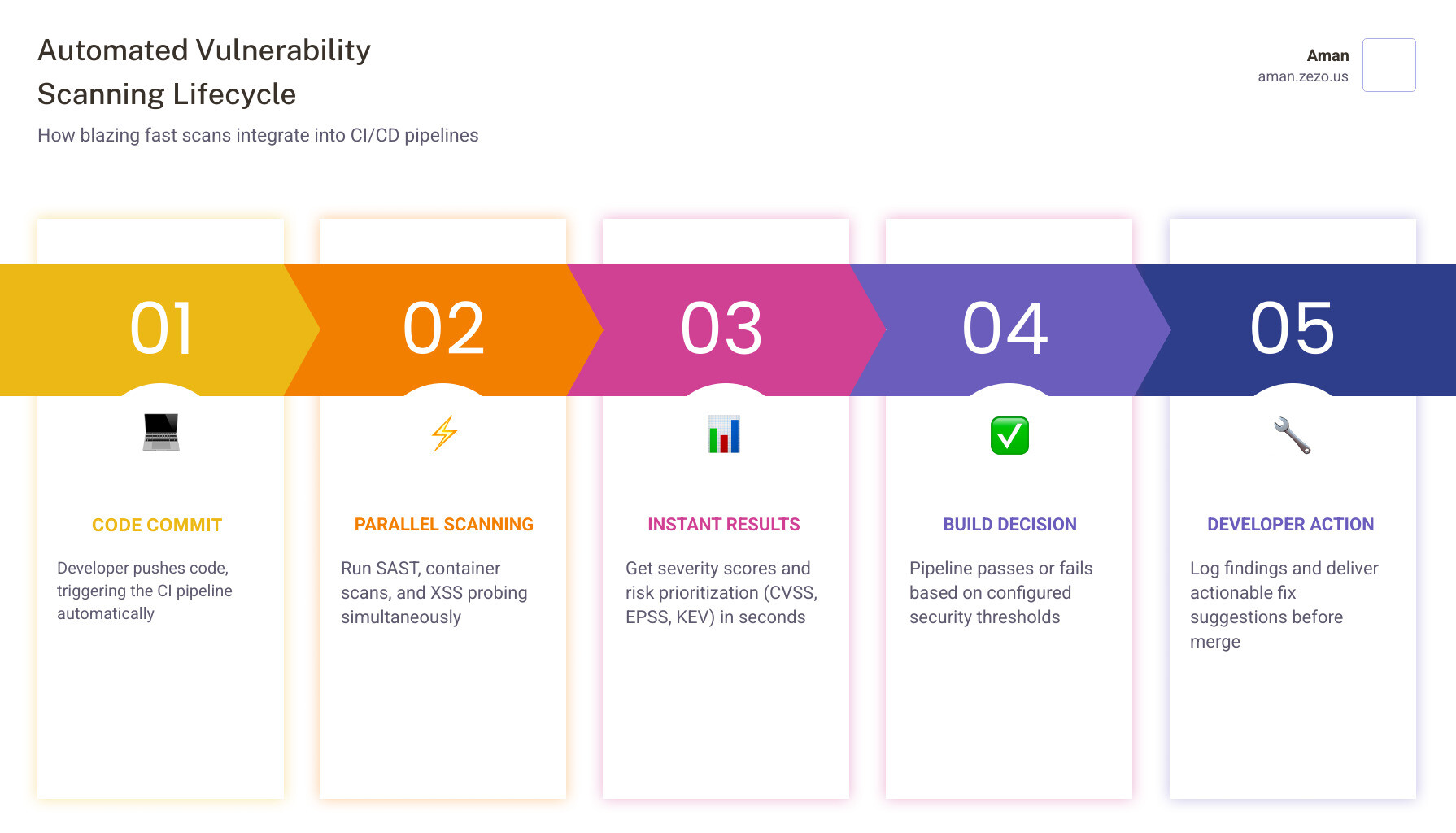
Why Your DevSecOps Pipeline Needs a Blazing Fast Vuln Scanner

In the past, security was a “gatekeeper.” You finished your code, sent it to the security team, and waited three days for a PDF report. In a modern DevSecOps world, that doesn’t work. If a scan takes 30 minutes, it breaks the developer’s “flow state.” If it takes 10 seconds, it’s just another part of the build process.
What makes a blazing fast vuln scanner actually fast? It usually comes down to three technical innovations:
- Asynchronous Programming: Instead of sending one request and waiting for a response before sending the next, modern tools send thousands of requests simultaneously. This allows a scanner to saturate available bandwidth rather than idling on CPU cycles.
- Single Request Multi Parameter Probing (SRMPP): This is a game-changer for web testing. Traditional scanners test parameters one by one. If a page has 50 parameters, it sends 50 requests. SRMPP-enabled tools like xssprober inject unique payloads into all parameters in a single request, reducing traffic and time by orders of magnitude.
- Resource Optimization: Using languages like Rust or Go allows tools to handle high-concurrency tasks with minimal memory overhead. For example, some scanners can process 100,000 lines of code in under 5 seconds by utilizing parallel processing and memory-mapped file reading.
Without these optimizations, you’re just adding technical debt to your security stack. Fast scanning is also a prerequisite for effectively fighting Cross-Site Scripting, where the sheer number of potential injection points can overwhelm slower, legacy tools.
3 Specialized Tools for Instant Security Audits
Generic scanners are great, but they often struggle with specialized environments like AI codebases or complex container registries. To truly achieve a “shift-left” security posture, we need engines that are extensible and rule-driven. By using custom YAML rules and extensible plugins, these three tools allow you to tailor your security checks to your specific tech stack.
For those looking for a broader suite of capabilities, you can explore more info about security tools to see how these specialized engines integrate into larger management platforms.
aiscan: The Blazing Fast Vuln Scanner for AI and LLM Risks
As every company rushes to integrate Large Language Models (LLMs), a new attack surface has emerged. aiscan is a specialized, Rust-powered CLI tool designed specifically to inventory AI usage and audit it for security risks.
What makes it a blazing fast vuln scanner?
- Tree-sitter Parsing: It uses tree-sitter for AST-based (Abstract Syntax Tree) scanning. This allows it to understand the structure of code across 500+ languages without the overhead of a full compiler.
- Parallel Processing: Using the Rayon library, it scans 100,000 lines of code in under 5 seconds.
- AI-Specific Checks: It audits for the OWASP LLM Top 10, including prompt injection risks and sensitive information disclosure.
- Cost Guardrails: Beyond security, it enforces token budgets and spend limits (max_usd), ensuring your AI implementations don’t accidentally bankrupt the company.
xssprober: A Blazing Fast Vuln Scanner for Web Entry Points
If you’ve ever run a traditional XSS scanner, you know the pain of waiting for it to crawl every single link and test every single input field. xssprober was built with a different philosophy: scan as much as possible, as quickly as possible.
The secret sauce here is the SRMPP technique. In a standard scan, time is calculated as (Request Time × Number of Payloads) × (Number of Parameters). With xssprober, the number of parameters is removed from the equation. The scan time is essentially just (Number of Payloads × Request Time).
It excels at:
- Hidden Parameter Discovery: Finding parameters that aren’t visible in the HTML but are processed by the backend.
- Asynchronous Probing: Handling massive lists of targets without slowing down.
- Independent Scaling: Whether a page has 2 inputs or 200, the scan takes the same amount of time.
Grype: Rapid Container and Supply Chain Analysis
Container security is often the slowest part of a CI/CD pipeline because images are heavy. Grype solves this by being exceptionally lightweight and smart about how it looks for vulnerabilities.
Key features include:
- SBOM-First Workflow: Instead of scanning a 1GB image every time, you can generate a Software Bill of Materials (SBOM) once using a tool like Syft. Grype can then scan that tiny JSON file in seconds.
- Advanced Prioritization: It doesn’t just give you a list of “High” or “Critical” bugs. It integrates EPSS (Exploit Prediction Scoring System) and the KEV (Known Exploited Vulnerabilities) catalog. This helps you focus on bugs that are actually being exploited in the wild, rather than theoretical risks.
- Daily Updates: It pulls from a SQLite database that updates daily, ensuring you’re protected against the very latest CVEs.
Performance Benchmarks: Real-World Speed Results
To understand the impact of a blazing fast vuln scanner, we have to look at the numbers. Statistics from real-world deployments show that moving from legacy engines to optimized ones can save thousands of CPU hours. For instance, the Yargo engine (a pure Go implementation of YARA) demonstrated a 6.8x speedup, cutting median scan times from 12.5 minutes down to under 2 minutes.
These benchmarks prove that speed isn’t just about finishing the build faster; it’s about accuracy. When a scanner is fast, you can run more rules. When you can run more rules, you find more bugs. This is particularly vital in Static Application Security Testing, where the complexity of modern codebases often leads to “scan fatigue” if the tools are too sluggish.
Strategic Integration: Scaling Without Triggering WAFs
One of the biggest risks of using a blazing fast vuln scanner is that it can look like a Distributed Denial of Service (DDoS) attack to a Web Application Firewall (WAF). If you send 5,000 requests in a second, you’re going to get blocked.
Strategic integration means being smart about how you deploy that speed:
- Recursive Crawling: Tools should intelligently discover entry points (forms, links, and data fields) before firing payloads.
- Parallel Processing vs. Rate Limiting: You want to process files in parallel on your local machine, but you may need to throttle the requests sent to the target server to avoid being banned.
- JSON Output: Fast scanners should always output in machine-readable formats like JSON or SARIF. This allows them to be piped into management platforms for triage.
- False Positive Reduction: Speed is useless if you have to spend three hours manually verifying the results. Modern tools use “context-aware” scanning to ensure that a reflected payload actually has the potential to execute.
Frequently Asked Questions about Fast Scanning
How does SRMPP reduce scan times?
Single Request Multi Parameter Probing (SRMPP) works by bundling multiple test payloads into a single HTTP request. Instead of testing “First Name,” then “Last Name,” then “Email” separately, the scanner puts a unique identifier in all three at once. If the server reflects one of those identifiers, the scanner knows exactly which parameter is vulnerable based on the unique ID it received back. This reduces the number of HTTP requests by 90% or more on complex forms.
Can fast scanners detect zero-day vulnerabilities?
While most scanners rely on known signatures (CVEs), advanced scanning engines allow you to write custom YAML templates. If a new vulnerability is announced (like Log4Shell), the community often releases a template within hours. Because these scanners are “blazing fast,” you can scan your entire infrastructure for that specific zero-day in minutes rather than days.
Why is SBOM scanning faster than image scanning?
Scanning a container image requires the tool to pull the image, extract the layers, and traverse the entire filesystem to find binaries. An SBOM is a pre-generated manifest of everything inside that image. Scanning an SBOM is just a text-parsing and database-lookup task, which is nearly instantaneous compared to the heavy lifting of image extraction.
Conclusion
At Aman, we believe that security should be a facilitator, not a roadblock. Our mission is to make exploitation so expensive and difficult for attackers that they simply give up. We achieve this by providing a blazing fast vuln scanner architecture within a comprehensive, free platform.
Our platform integrates over 50 specialized scanners — including the types of high-speed engines discussed here — to give you instant AI-powered explanations and actionable fix suggestions. Whether you are a bug bounty hunter or a DevSecOps engineer, you shouldn’t have to choose between speed and security.
Start your free security audit today and see how fast your security workflow can truly be.
Secure Your Apps with Aman
Put these mitigation steps into practice. Get professional-grade vulnerability detection in one place.
Launch Your First Scan Now