
How To Mitigate SQL Injection Vulnerabilities
How to mitigate sql injection vulnerabilities
SQL injection remains one of the most dangerous and prevalent security vulnerabilities in web applications today. Despite being a well-known attack vector, SQL injection continues to rank among the top security risks, causing data breaches that expose millions of sensitive records annually. For businesses, security professionals, and developers, understanding how to effectively mitigate these vulnerabilities is crucial for maintaining robust cybersecurity posture and protecting valuable data assets.
SQL injection occurs when malicious SQL code is inserted into application queries, allowing attackers to manipulate database operations, extract sensitive information, modify data, or even gain administrative control over systems. The consequences can be devastating, ranging from data theft and financial losses to regulatory penalties and irreparable damage to business reputation.
Understanding SQL Injection Attack Vectors
Before implementing mitigation strategies, it’s essential to understand how SQL injection attacks work and the various forms they can take. Classic SQL injection involves directly manipulating SQL queries through user input fields, while blind SQL injection exploits applications that don’t display database errors but still execute malicious queries.

Common attack scenarios include:
- Login bypass attempts where attackers use malicious input to circumvent authentication
- Data extraction attacks that retrieve sensitive information from databases
- Second-order injections that store malicious payloads for later execution
- Time-based attacks that infer database structure through response delays
Attackers typically target vulnerable input fields such as login forms, search boxes, contact forms, and URL parameters. Any application component that processes user input and constructs SQL queries without proper validation becomes a potential entry point for injection attacks.
Implementing Parameterized Queries and Prepared Statements
The most effective defense against SQL injection is the use of parameterized queries and prepared statements. This approach separates SQL code from user data, ensuring that input is treated as data rather than executable code.
Prepared statements work by pre-compiling SQL queries with placeholder parameters. When user input is provided, it’s bound to these parameters without being interpreted as SQL code. This fundamental separation makes SQL injection attacks virtually impossible, as the database engine treats all input as literal data values.
Implementation best practices for prepared statements include using appropriate data type binding, ensuring all dynamic content is parameterized, and avoiding string concatenation for query construction.
Different programming languages and frameworks provide various implementations of prepared statements. Java offers PreparedStatement classes, PHP provides PDO prepared statements, and .NET includes SqlCommand with parameters. Regardless of the technology stack, the principle remains the same: separate code from data through parameterization.
Input Validation and Sanitization Techniques
While parameterized queries provide the strongest defense, implementing comprehensive input validation adds an essential additional security layer. Input validation should occur at multiple levels, including client-side validation for user experience and server-side validation for security enforcement.
Effective validation strategies include:
- Whitelist validation that accepts only known-good input patterns
- Data type validation ensuring input matches expected formats
- Length restrictions preventing buffer overflow attempts
- Character encoding validation to prevent bypass techniques
Sanitization processes should escape special characters that have meaning in SQL contexts. However, it’s important to note that sanitization alone is insufficient and should never be relied upon as the primary defense mechanism. Attackers continuously develop new bypass techniques that can circumvent sanitization filters.
Regular expression validation can help enforce input format requirements, but care must be taken to avoid overly complex patterns that might introduce performance issues or create new vulnerabilities through regex injection attacks.
Database Security Configuration and Access Controls
Proper database configuration significantly reduces the impact of successful SQL injection attacks. Implementing the principle of least privilege ensures that application database accounts have only the minimum permissions necessary for legitimate operations.
Essential database security measures include:
- Creating dedicated application accounts with restricted privileges
- Removing or disabling unnecessary database features and stored procedures
- Implementing network-level access controls and firewall rules
- Enabling database activity monitoring and logging
- Regular security updates and patch management
Database account permissions should be carefully reviewed to ensure applications cannot perform administrative functions like creating users, modifying system tables, or accessing sensitive configuration data. Stored procedures can provide an additional security layer when properly implemented with parameterized inputs, though they should not be considered a complete solution.
Network segmentation isolates database servers from direct internet access, requiring attackers to compromise multiple systems before reaching critical data repositories. This defense-in-depth approach significantly increases the complexity and detectability of successful attacks.
Web Application Firewalls and Security Testing
Web Application Firewalls (WAFs) provide real-time protection against SQL injection attempts by analyzing HTTP requests and blocking suspicious patterns. While WAFs offer valuable protection, they should complement, not replace, secure coding practices and proper application design.
Modern WAF solutions use machine learning algorithms to identify attack patterns and adapt to new threat vectors. However, signature-based detection can be bypassed through encoding techniques and novel attack methods, making regular updates and tuning essential for effectiveness.
Comprehensive security testing strategies should include:
- Static application security testing (SAST) during development
- Dynamic application security testing (DAST) against running applications
- Interactive application security testing (IAST) for runtime analysis
- Regular penetration testing by qualified security professionals
Automated vulnerability scanners can identify common SQL injection vulnerabilities, but manual testing remains crucial for discovering complex logical flaws and business logic vulnerabilities. The OWASP Top 10 provides valuable guidance on current web application security risks and mitigation strategies.
Monitoring, Incident Response, and Continuous Improvement
Effective SQL injection mitigation requires ongoing monitoring and incident response capabilities. Database activity monitoring tools can detect unusual query patterns, failed login attempts, and other indicators of potential attacks in progress.
Security Information and Event Management (SIEM) systems aggregate logs from various sources to provide comprehensive visibility into security events. Behavioral analysis capabilities can identify anomalous database access patterns that might indicate successful compromise or ongoing attack attempts.
Incident response procedures should address SQL injection scenarios specifically, including steps for containing attacks, assessing damage, and implementing recovery measures. Regular tabletop exercises help ensure response teams are prepared to handle actual incidents effectively.
Continuous improvement processes should incorporate lessons learned from security incidents, threat intelligence updates, and emerging attack techniques. According to the National Vulnerability Database, new SQL injection variants are discovered regularly, making ongoing vigilance essential.
Conclusion
Mitigating SQL injection vulnerabilities requires a comprehensive, multi-layered approach that combines secure coding practices, robust input validation, proper database configuration, and continuous monitoring. While the threat landscape continues to evolve, the fundamental principles of parameterized queries, input validation, and defense-in-depth remain the cornerstone of effective protection.
Organizations must prioritize security awareness training for development teams, implement automated security testing throughout the development lifecycle, and maintain current knowledge of emerging threats and mitigation techniques. By following established security frameworks such as those provided by SANS Institute, businesses can significantly reduce their exposure to SQL injection attacks and protect their valuable data assets.
Regular security assessments, penetration testing, and vulnerability management programs ensure that protective measures remain effective against evolving attack techniques. With proper implementation and ongoing maintenance, SQL injection vulnerabilities can be effectively mitigated, providing organizations with the security foundation necessary for safe digital operations.
Accelerate Your Security Assessments with Aman
Automated security tools deliver the speed and consistency your team needs to identify vulnerabilities before attackers do. If you are ready to move beyond slow manual scans and overwhelmed reporting, Aman provides an all-in-one vulnerability scanner and penetration testing platform that matches the article’s vision of faster, safer assessments. With 51 integrated scanning and penetration tools, Aman simplifies your workflow while improving coverage across applications, services, and infrastructure.
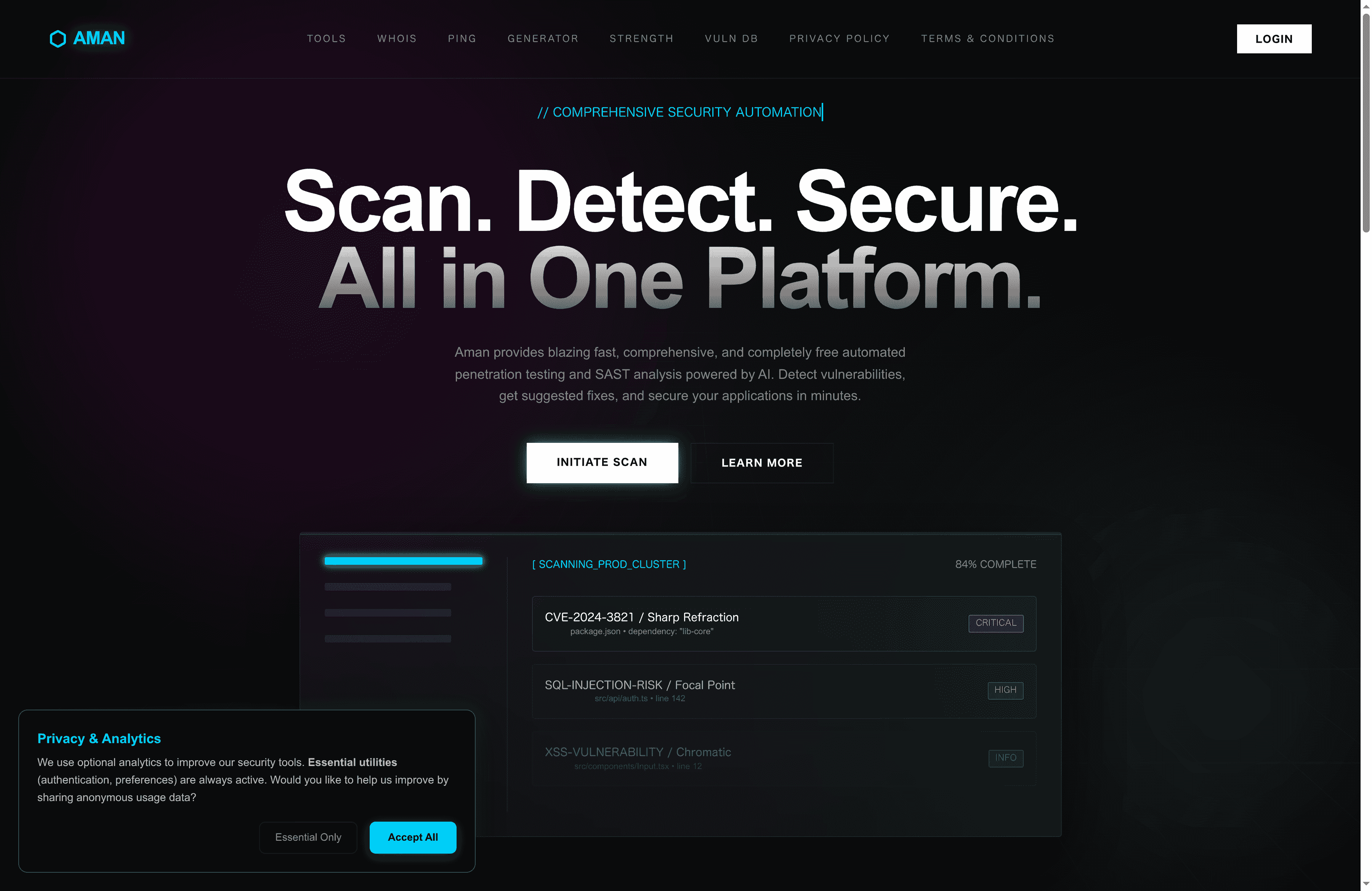
Experience comprehensive, continuous scanning with intelligent reporting designed to reduce false positives and prioritize critical risks. Whether you are a security analyst, DevOps engineer, or penetration tester, Aman empowers you to focus on analysis and remediation rather than repetitive grunt work. Start securing your environment today by visiting Aman and discover how our platform delivers the speed, coverage, and reporting capabilities your team needs for proactive vulnerability management.
Recommended
- Aman – Security Scanner
- Aman – Security Scanner Tools
- Aman – Security Scanner Vulnerabilities Database
- Aman – Security Scanner Password Strength Checker
Secure Your Apps with Aman
Put these mitigation steps into practice. Get professional-grade vulnerability detection in one place.
Launch Your First Scan Now